Azure Active Directory Authentication
Instructions for setting up Azure Active Directory authentication with Seq
Seq can authenticate users in Microsoft Azure Active Directory. This makes it easier for organizations to centrally manage user accounts.
When this configuration is enabled, users will be redirected to an external Azure Active Directory sign-in page to authenticate when logging into Seq.
Before you begin...
Popular browsers, including Chrome, will no longer send cross-site authentication cookies unless the request is secure (HTTPS).
If you're running Seq on Windows, you'll need to configure Seq with an SSL certificate before setting up OIDC.
On Docker/Linux, you'll need to configure SSL termination at a load balancer/reverse proxy/ingress, and set the
SEQ_API_CANONICALURIenvironment variable in the container to Seq's public HTTPS address.
Getting started
The first step to enable AAD authentication in Seq is to open Settings > System and choose Enable Authentication.
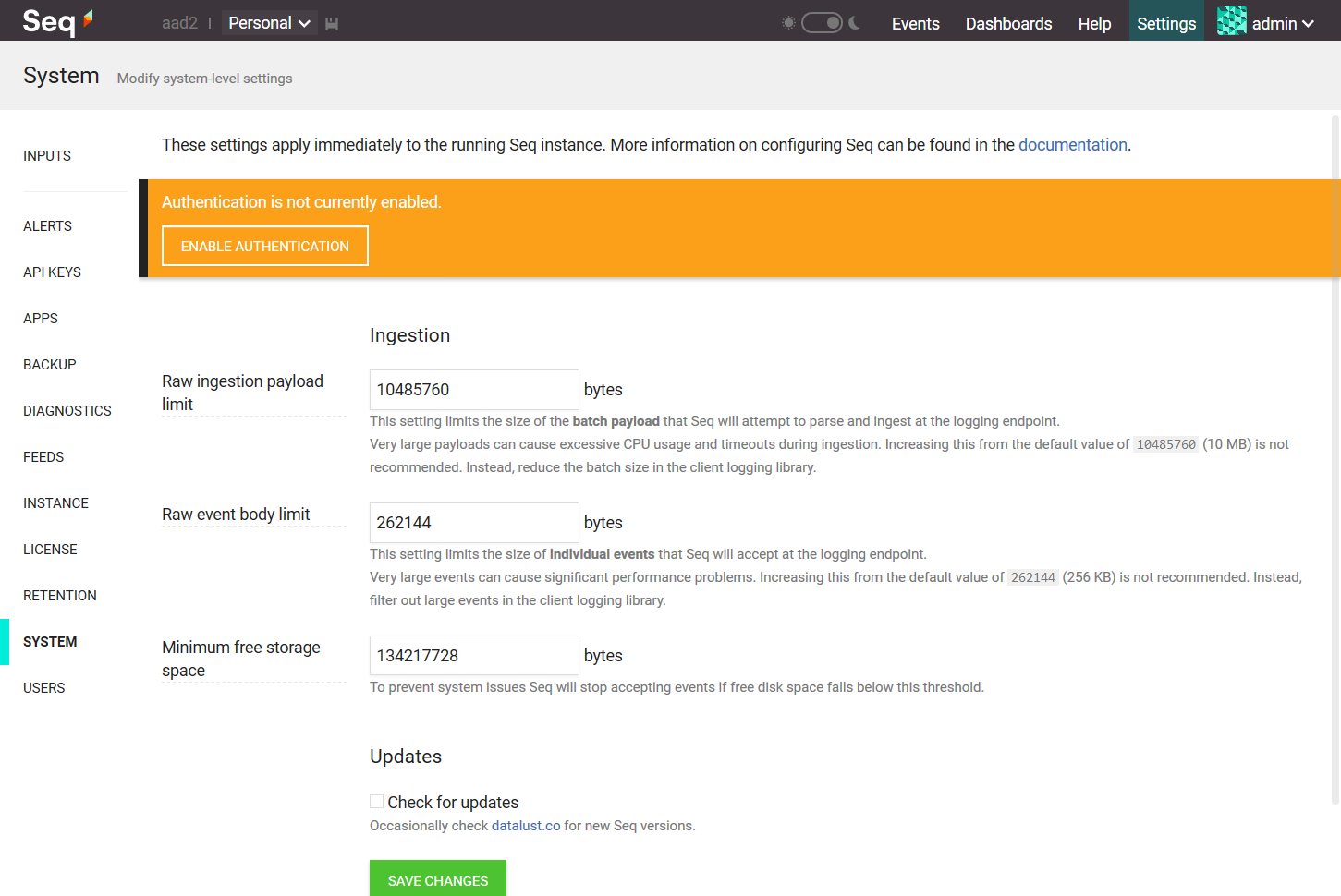
If you've already enabled a different authentication provider, click Change beside the authentication provider edit box.
Preserving Existing User Accounts
If you have existing user accounts that you want to link and continue using with AAD, please contact Support for migration assistance.
Seq will load the Enable Authentication screen.
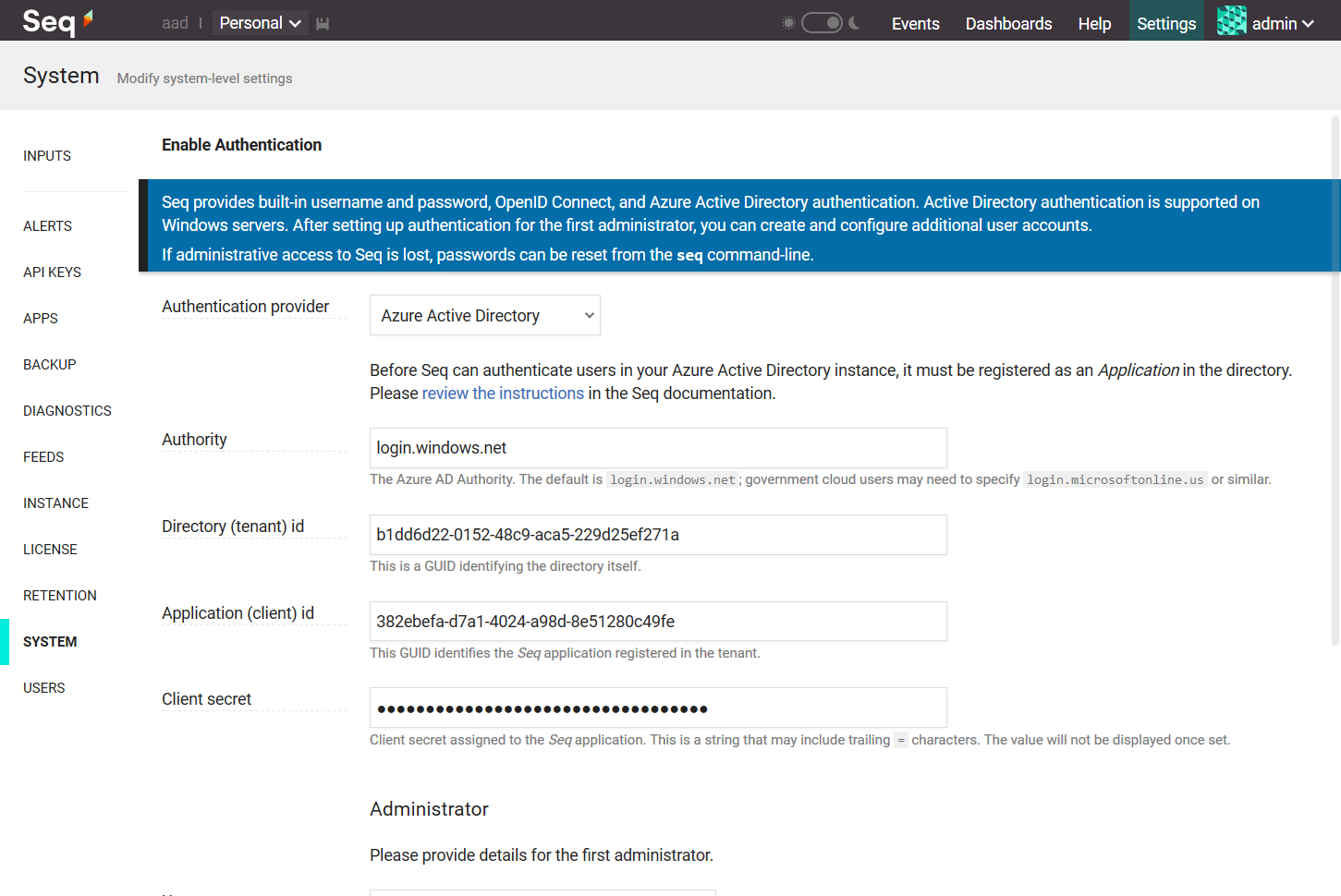
Choose Azure Active Directory from the Authentication Provider drop-down. This will show some edit boxes for the various pieces of information we'll collect from the Azure Portal.
Registering Seq as an application in Azure Portal
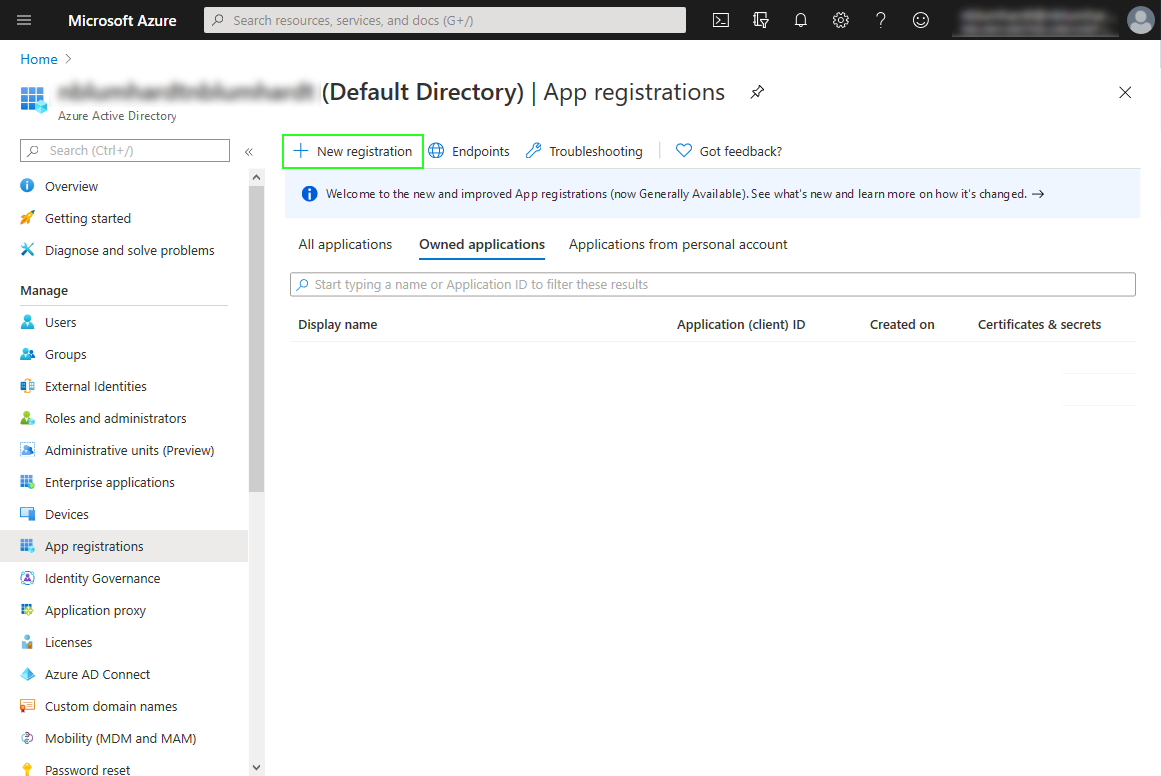
In the App registrations screen, choose New app registration:
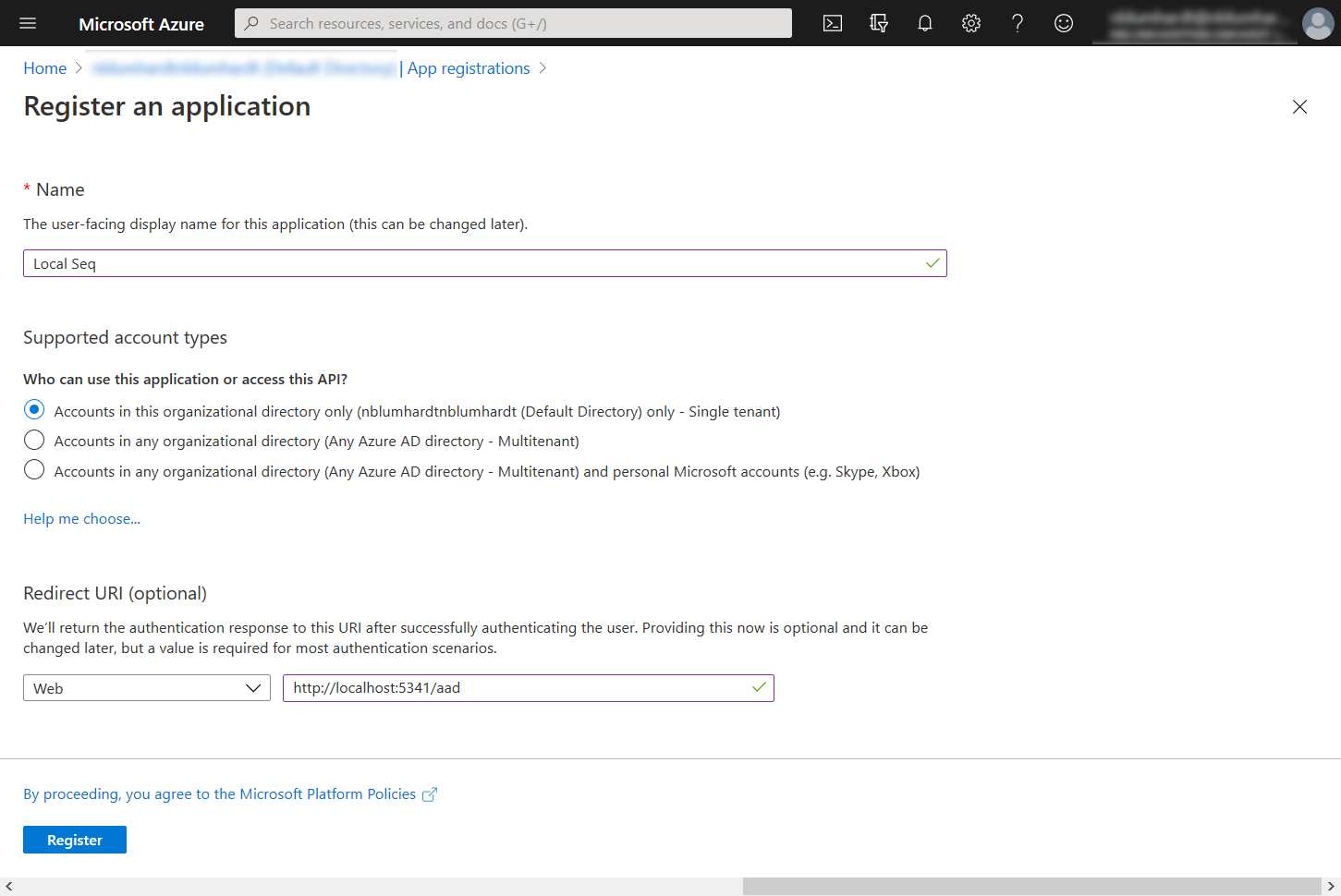
You can call the application anything you like that will help you to identify it.
Although the heading states that the redirect URI is optional, you must add the address of your Seq instance, with /aad appended, here:
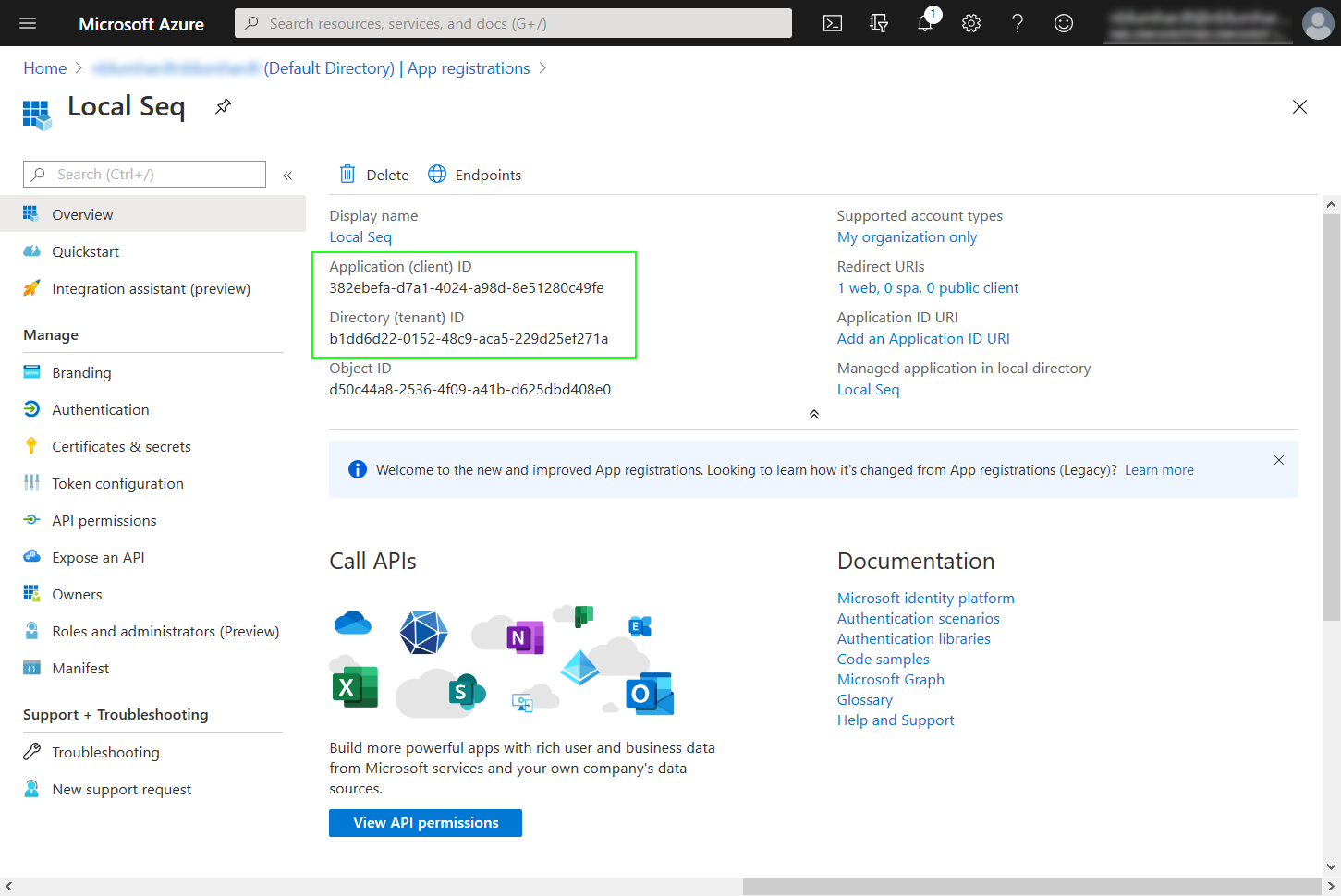
This will show the application's identifiers. Copy the Application ID and Directory ID values into the corresponding fields in Seq:
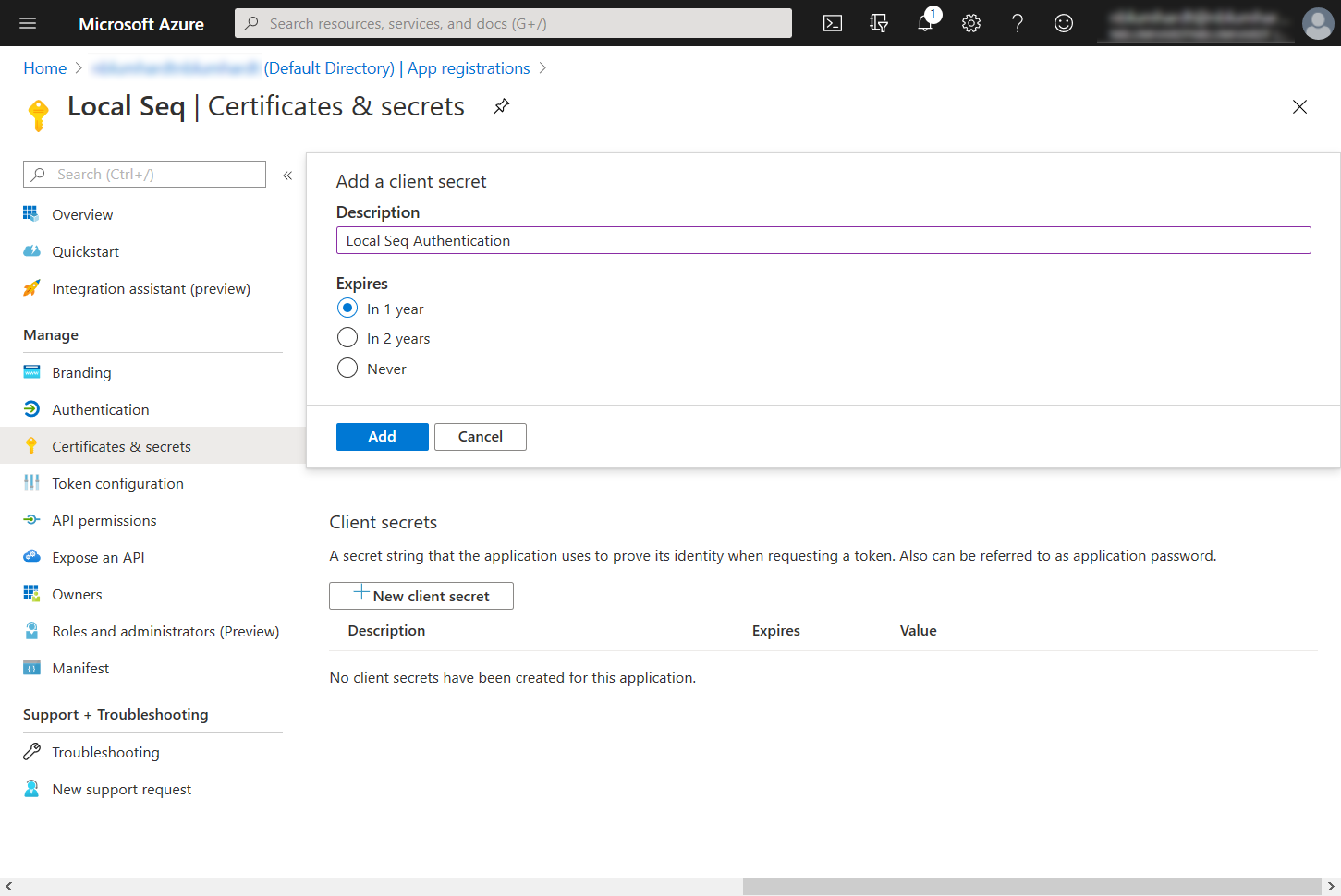
Under Certificates and Secrets, create a new client secret and copy it into the corresponding field in Seq:
Your Enable Authentication screen in Seq should now look like:
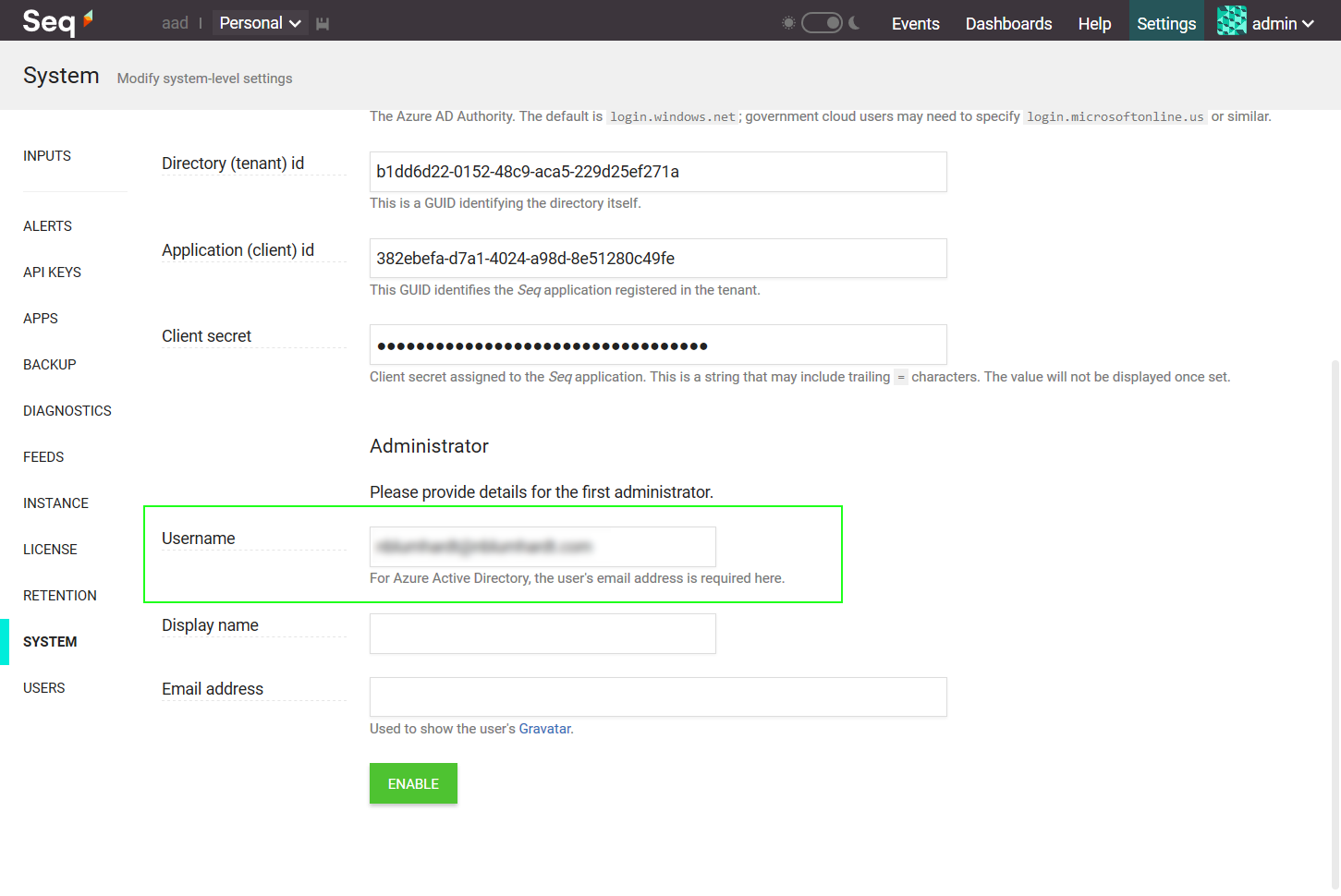
Finally, set the Administrator Username field in Seq to the email address of a user in the directory, and click Enable:
You'll be logged out of Seq, and should be presented with the Seq login screen:
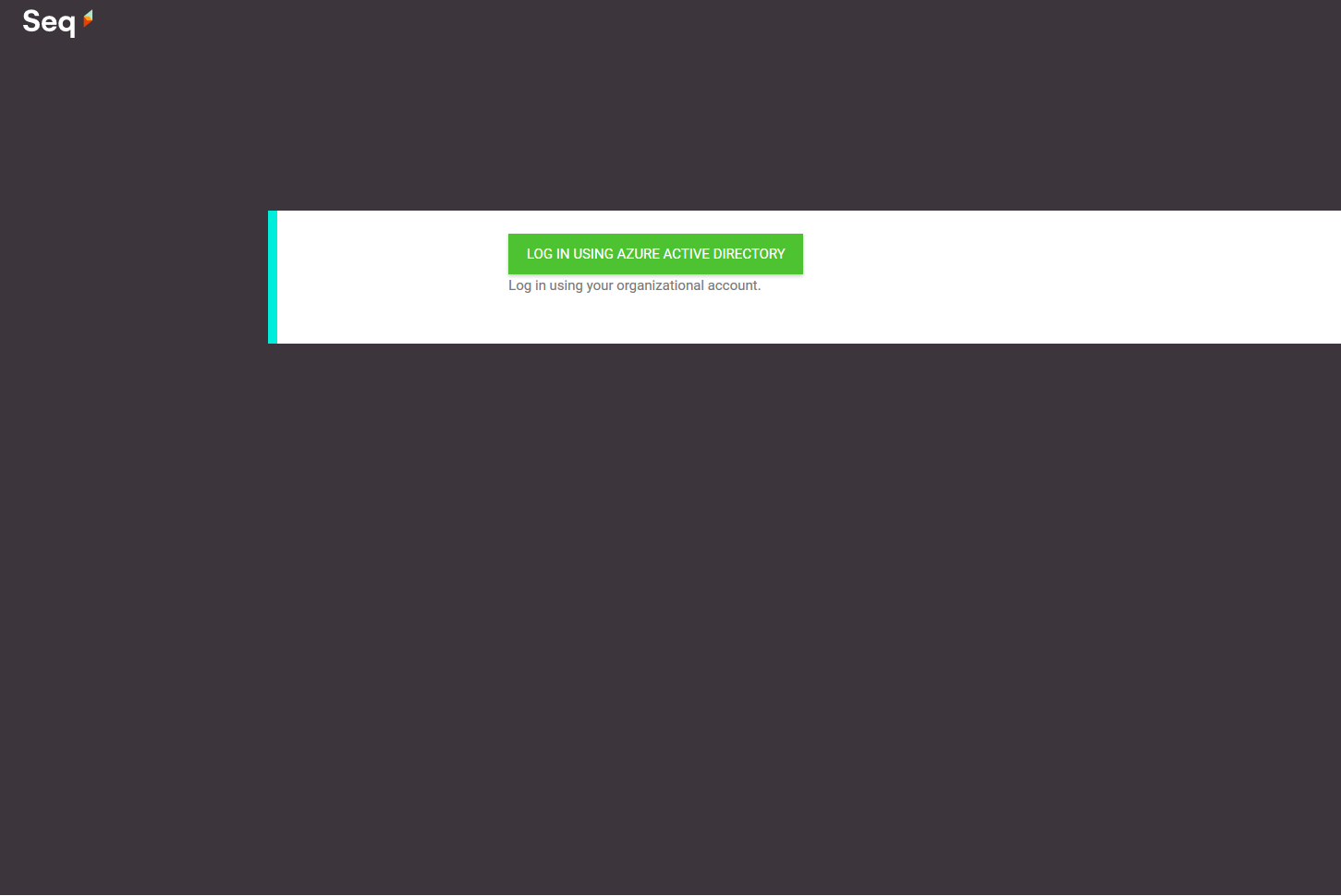
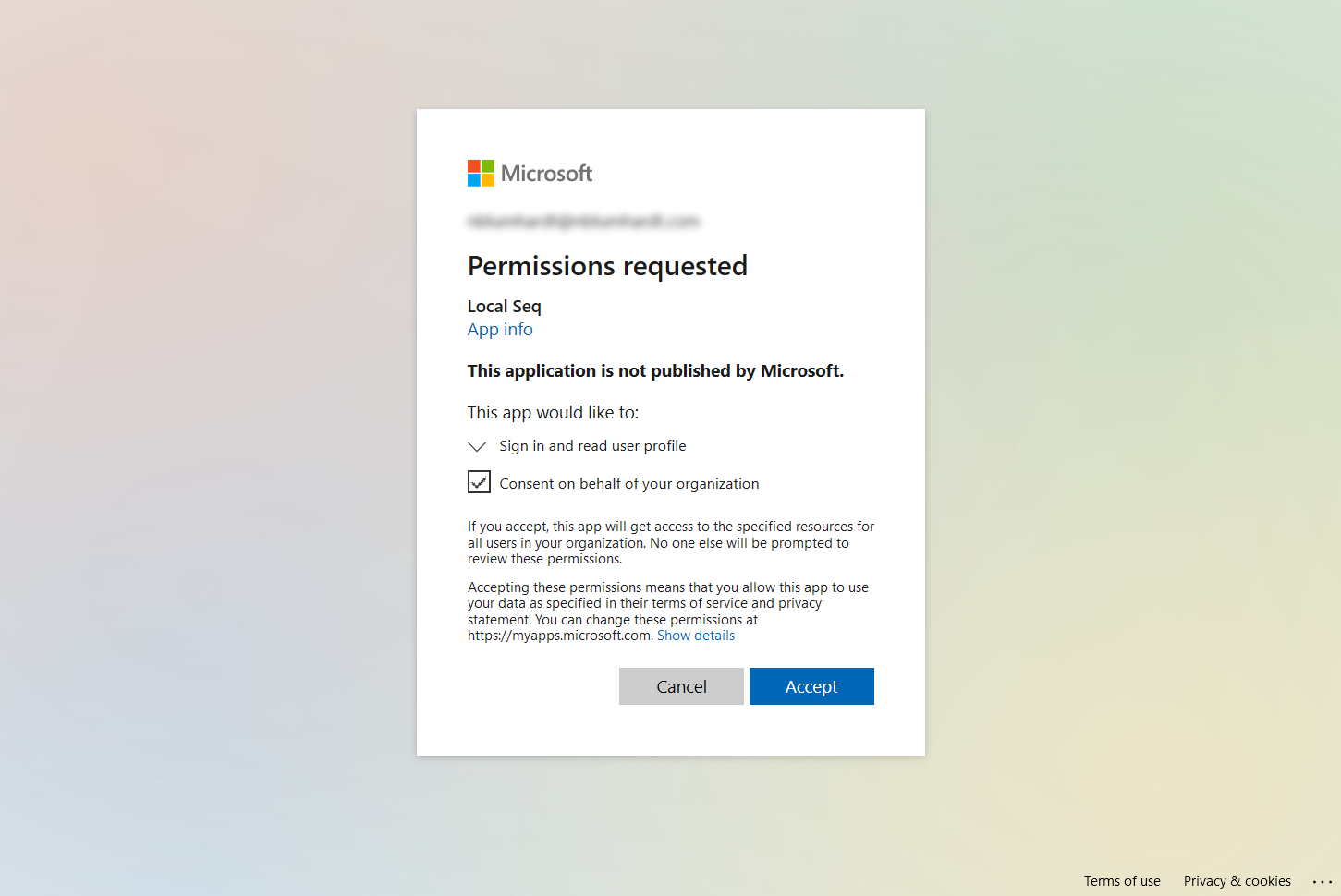
When you click Log in using Azure Active Directory, you'll be asked to give the application access to your AAD account information.
Finally, you'll be redirected back to Seq, logged in as the admin user.
If you lose access...
AAD configuration can sometimes be tricky. If you made a mistake in the final step, you can reset Seq to use Basic authentication from the command-line on the Seq server.
seq.exe service stop seq.exe auth --basic -u "yourusername" -p "yourpassword" seq.exe service startYou must specify the
--storage=argument toseq.exe authif a custom storage location is in use.If you continue to have trouble, we're here to help - please contact us for support.
Add Users
Seq won't automatically provision accounts for users in your directory. To do this, please go to Settings > Users and add users as required.
When adding users to Seq, the Username for the user is the email address that's used when logging in to AAD.
Updated 5 months ago
