HTTPS (TLS/SSL)
Production Seq deployments should enable HTTPS to secure the user interface and web API.
Seq fully supports HTTPS on Windows. To enable HTTPS, you'll need a valid SSL certificate that matches the hostname of your Seq server.
For TLS to provide effective security, you need to ensure that both the apps writing log events, and the client machines used to browse to Seq web user interface, trust the certificate assigned to the Seq server.
It is possible to disable certificate validation in apps, or ignore certificate validation warnings in web browsers, but in both of these cases it is unlikely TLS provides any material protection against an observer intercepting communication with the server.
Installing your SSL certificate
Seq automatically searches the Local Computer\Personal certificate store for SSL certificates that:
- Match the hostname portion of the HTTPS URI Seq is configured to serve traffic for; e.g. if
https://seq.example.comis configured in the installation wizard, Seq will look for a certificate with subjectCN=seq.example.com("Issued to"seq.example.com), and - That include a private key.
To install or inspect your SSL certificates, open certlm.msc and navigate to the Personal\Certificates folder:
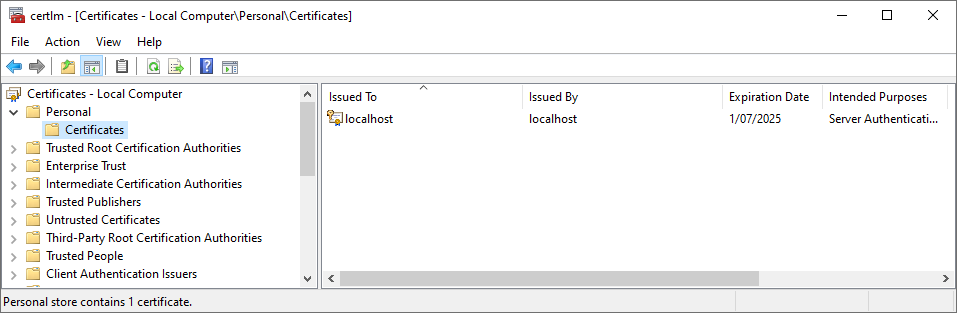 Only the certificates visible in this folder will be available to Seq.To import your certificate, right-click on the folder and choose All Tasks, Import....
Only the certificates visible in this folder will be available to Seq.To import your certificate, right-click on the folder and choose All Tasks, Import....
Setting an HTTPS listen URI
Once your certificate is imported, from the Start menu, open Seq Service Administration.
On the second screen, update the Listen URI field to include the https:// address of your Seq instance.
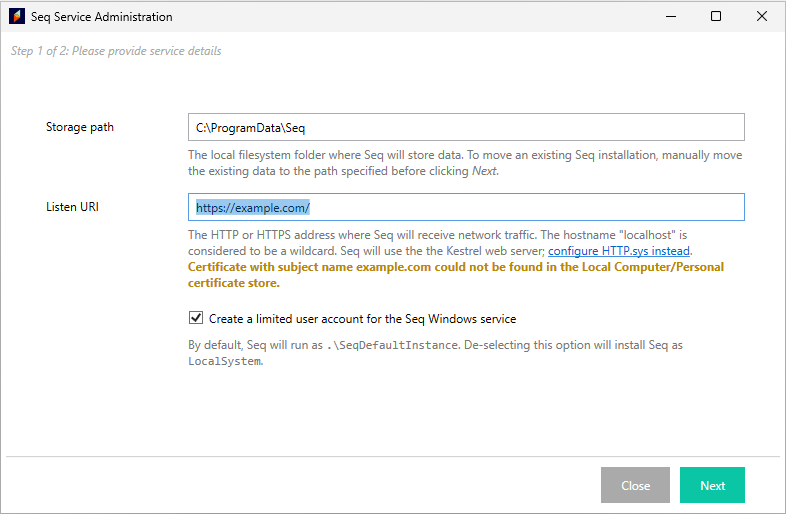
If the wizard shows a warning as it does in the screenshot above, go back and check that the certificate in the Personal\Certificates folder has a subject (CN) that matches the given hostname (example.com in this example).
Once the wizard accepts the new URI without any warnings, press Next to complete setup.
Scripted/command-line configuration
If the Seq Service Administration UI cannot be used, the easiest way to script HTTPS setup is to use the HTTP.sys web server and the instructions for configuring HTTPS with HTTP.sys instead.
Updated 27 days ago
